Rapid Incident Response (IR)
A security incident is inevitable, but a crisis is optional. Our Incident Response team provides immediate, expert support and uses a structured, proven methodology to contain, eradicate, and recover from breaches with minimum business impact.
Leveraging XDR for Faster Containment
Our Incident Response team utilizes Extended Detection and Response (XDR) technology to accelerate threat detection, containment, and remediation. By integrating data from multiple security layers (endpoint, network, cloud, identity), XDR provides a holistic view of the attack surface, enabling faster identification of threats and more effective response actions.
- Automation: Automated first-step containment and data collection.
- Full Visibility: See the entire attack timeline across all domains (Cloud, Endpoint, Identity).
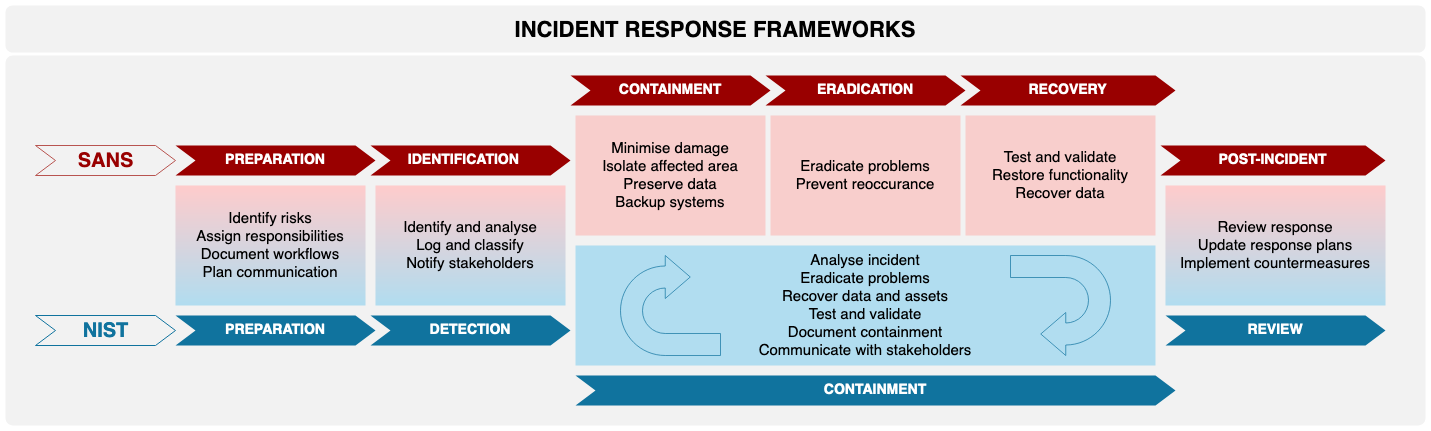
Our Proven Six-Step IR Life Cycle
1. Preparation
Develop plans, secure necessary contracts (retainer), and establish communication channels before an incident.
2. Identification
Verify the incident, gather forensic data, and determine the scope (who, what, where, when).
3. Containment
Limit the damage and prevent the attack from spreading (e.g., segmenting networks, isolating infected hosts).
4. Eradication
Completely remove the threat (malware, backdoors, rogue accounts) from the environment.
5. Recovery
Restore affected systems to normal operation, confirm full functionality, and monitor closely.
6. Lessons Learned
Document the incident, revise policies, and implement permanent changes to prevent recurrence.